The Next Evolution In Security Validation
Agentic AI Powered Offensive
Security Platform
Collaborative Reconnaissance, Coordinates Exploit Chaining and Dynamic Threat Modeling

From Automation to Agentic Security Validation
Showcase of the RidgeGen Agentic AI Framework
JWT has been behind some of the world’s most damaging enterprise attacks. See how the RidgeGen framework helps you detect and safely validate these attacks.

Click to learn more about the framework and a demo.
Fight smarter, not harder — use AI for your CTEM
Problem
“Infrequent pen testing leaves us exposed.”
Solution
RidgeBot® can shorten risk windows from months to minutes, identifying and validating vulnerabilities in real-time to close all security gaps.
Problem
“We’re resource-strapped to validate all systems.”
Solution
At 100x the speed of a human, RidgeBots® scalability enables simultaneous penetration testing of your entire IT assets – generating real-time reports in seconds.
Problem
“My own team lacks security testing experience.”
Solution
RidgeBot® bridges the security skills gap by automating security validation, enabling teams to perform penetration testing or simulate attacks without relying on specialized and costly resources.
Problem
“I need hard evidence to drive action and investment.”
Solution
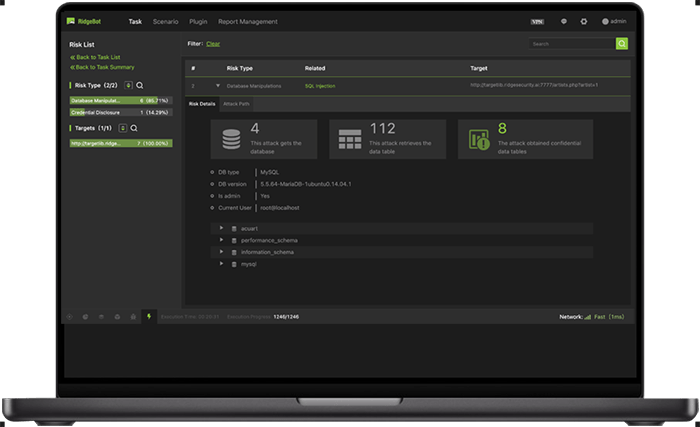
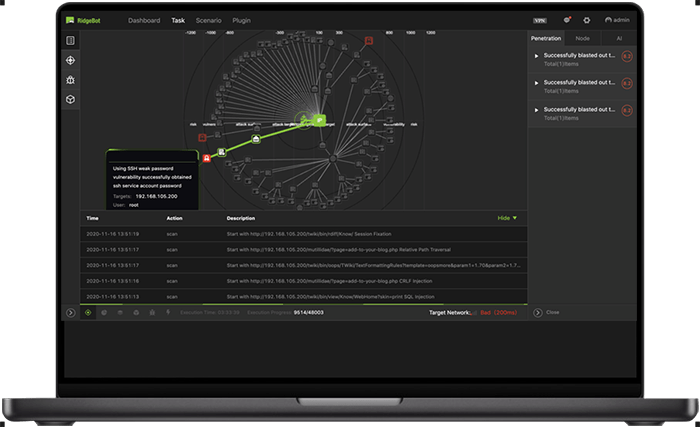
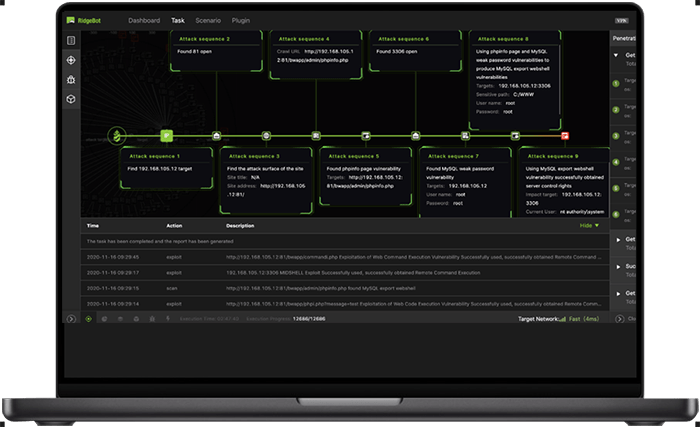
RidgeBot® provides detailed kill chain mapping that reveals actionable remediation insights. Its evidence-based reports clearly highlight security gaps and impacts, helping you justify security spend and investment.
RidgeBot® is the smart choice.
Powerful. Efficient. Proven.
RidgeBot®
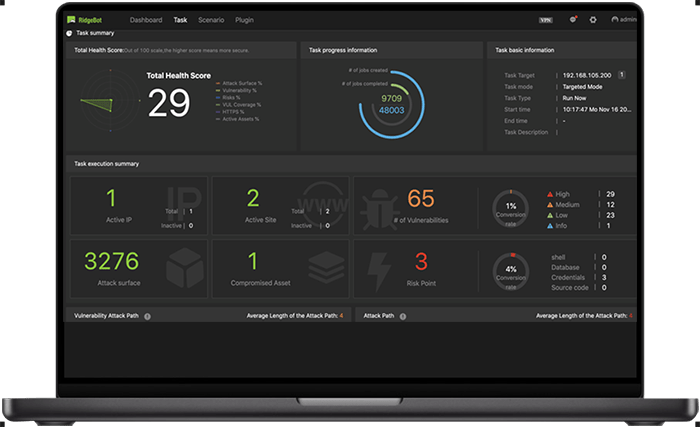
RidgeBots offensive security AI-powered threat validation ensures security teams focus on the threats that matter, eliminating guesswork and reducing response time.
Stop reacting—start preventing. RidgeBot’s security validation platform continuously validates your security posture, ensuring that only real threats demand attention. By eliminating false positives and automating threat validation, security teams can remediate vulnerabilities faster and stay ahead of evolving cyber risks.
See your risks before attackers do. RidgeBot autonomously maps your entire attack surface—networks, applications, APIs, and cloud—validating real vulnerabilities with zero false positives. Get real-time insights into exploitable weaknesses so your security team can act fast and stay ahead of threats.
Expand security testing without adding headcount.
RidgeBot operates as an AI-powered security agent, continuously validating vulnerabilities through safe exploit simulations. Automate large-scale security validation and offensive security testing to reduce costs, eliminate manual delays, and strengthen defenses fast.
RidgeBot® is the smart choice.
Powerful. Efficient. Proven.
RidgeBot®
RidgeBots offensive security AI-powered threat validation ensures security teams focus on the threats that matter, eliminating guesswork and reducing response time.
Optimize Defense
- Stop reacting—start preventing. RidgeBot continuously validates your security posture, ensuring that only real threats demand attention. By eliminating false positives and automating threat validation, security teams can remediate vulnerabilities faster and stay ahead of evolving cyber risks.
Improve Exposure Awareness
- See your risks before attackers do. RidgeBot autonomously maps your entire attack surface—networks, applications, APIs, and cloud—validating real vulnerabilities with zero false positives. Get real-time insights into exploitable weaknesses so your security team can act fast and stay ahead of threats.
Scale Offensive-Testing Capabilities
- Expand security testing without adding headcount. RidgeBot operates as an AI-powered security agent, continuously validating vulnerabilities through safe exploit simulations. Automate large-scale security testing and validation to reduce costs, eliminate manual delays, and strengthen defenses fast.
The CISOs trusted platform for automated security validation.
Act fast. Because delays mean breaches.
RidgeBots® offensive AI-powered threat validation ensures security teams focus on the threats that matter, eliminating guesswork and reducing response time.
36 Billion
Private record breaches
Source: Search Logistics 2024
$4.88 Million
Global average data breach cost
Source: Search Logistics 2024
50% of orgs carry critical security debt
Source: State of Software Security report 2025
48% of apps have critical OWASP Top 10 flaws
Source: State of Software Security report 2025
What the security community is saying about RidgeBot®
Recognized by the industry as leaders in AI-powered security validation

2026 AI-Powered Offensive Security Platform

Global Automated Security Validation Recognition
Cybersecurity Excellence Award

CRN's Tech Elite 250

Breakthrough Award AI in CTEM