SmarterTools recently confirmed that the Warlock (aka Storm-2603) ransomware group breached its network by exploiting an unpatched SmarterMail instance via CVE-2026-24423. The incident underscores a growing security concern: several SmarterMail vulnerabilities listed in CISA’s Known Exploited Vulnerabilities (KEV) catalog—including CVE-2025-52691 (CVSS 10.0), CVE-2026-23760 (CVSS 9.8), and CVE-2026-24423 (CVSS 9.3)—are already being actively exploited in the wild.
SmarterMail, a secure all-in-one email and collaboration server for Windows and Linux and an affordable Microsoft Exchange alternative, has become an attractive target for attackers. Because the software is open source, threat actors can closely monitor release notes and perform patch diffing to quickly identify exploitable weaknesses. With real-world attacks already underway, delaying updates is no longer a safe option—PATCH NOW.
Vulnerability Breakdowns
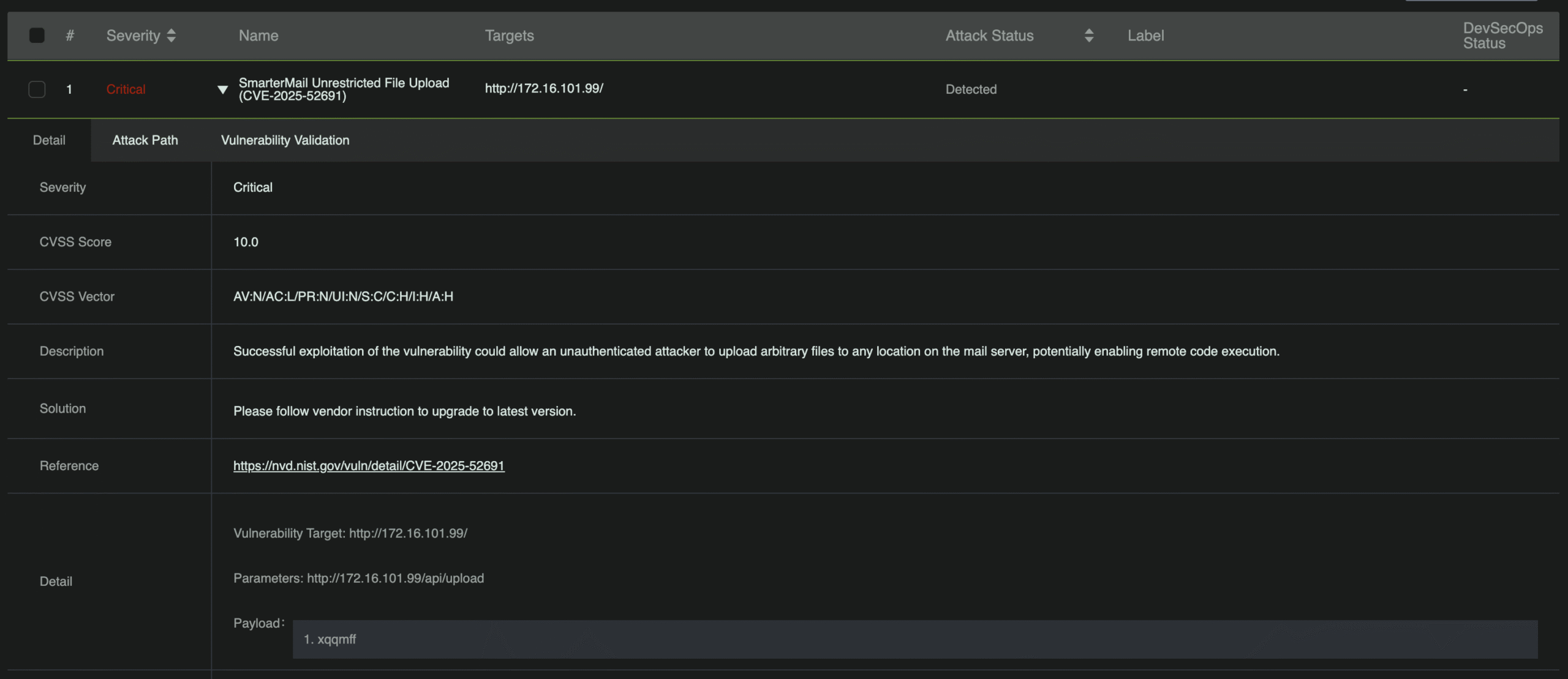
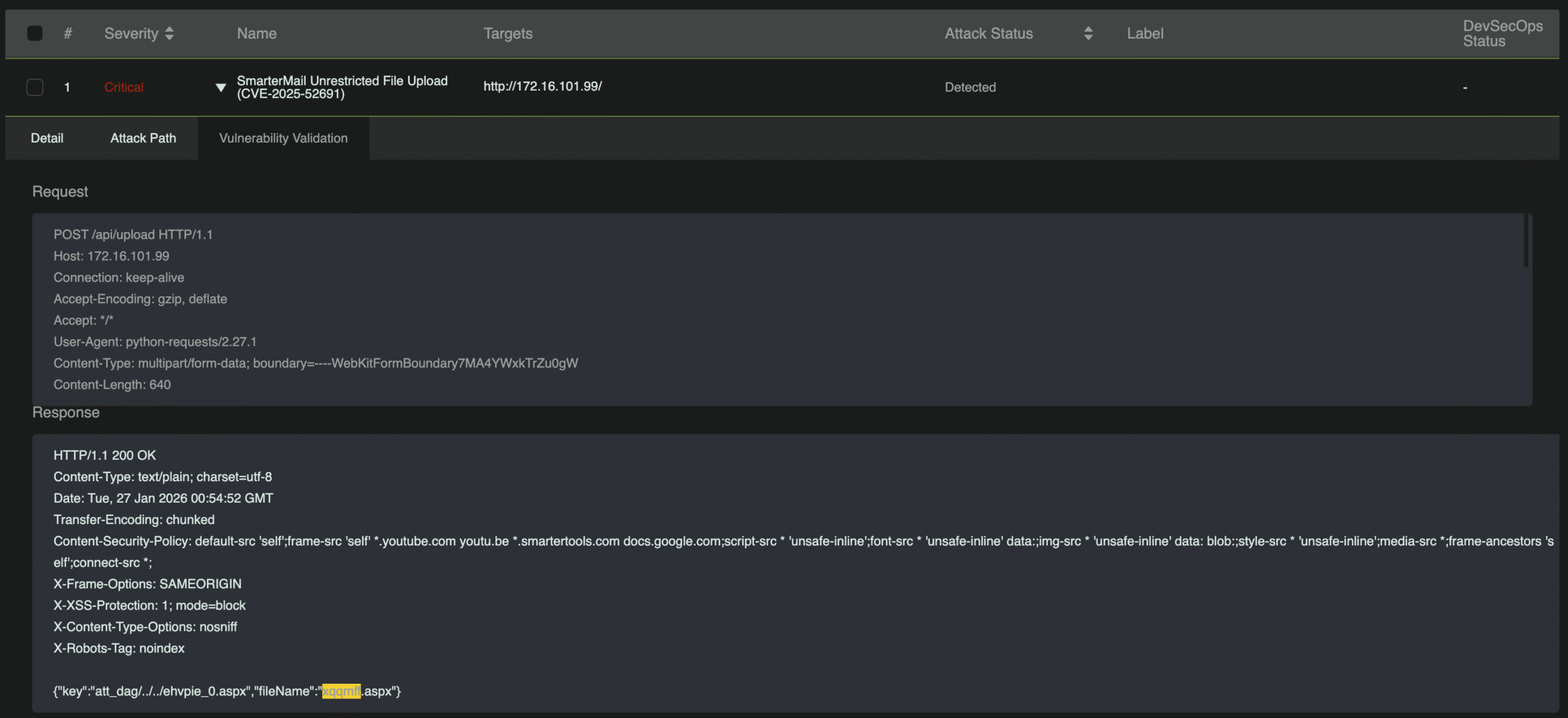
SmarterMail Unrestricted File Upload (CVE-2025-52691)
CVE-2025-52691 is a critical pre-authentication remote code execution vulnerability in SmarterMail stemming from an exposed /api/upload endpoint that allows anonymous file uploads. The flaw arises from insufficient validation of a user-controlled guid parameter within the upload workflow, enabling path traversal during attachment processing. By crafting a multipart request with malicious contextData, an attacker can escape the intended upload directory and write arbitrary files—such as a webshell—to sensitive locations, ultimately achieving full remote code execution without authentication.
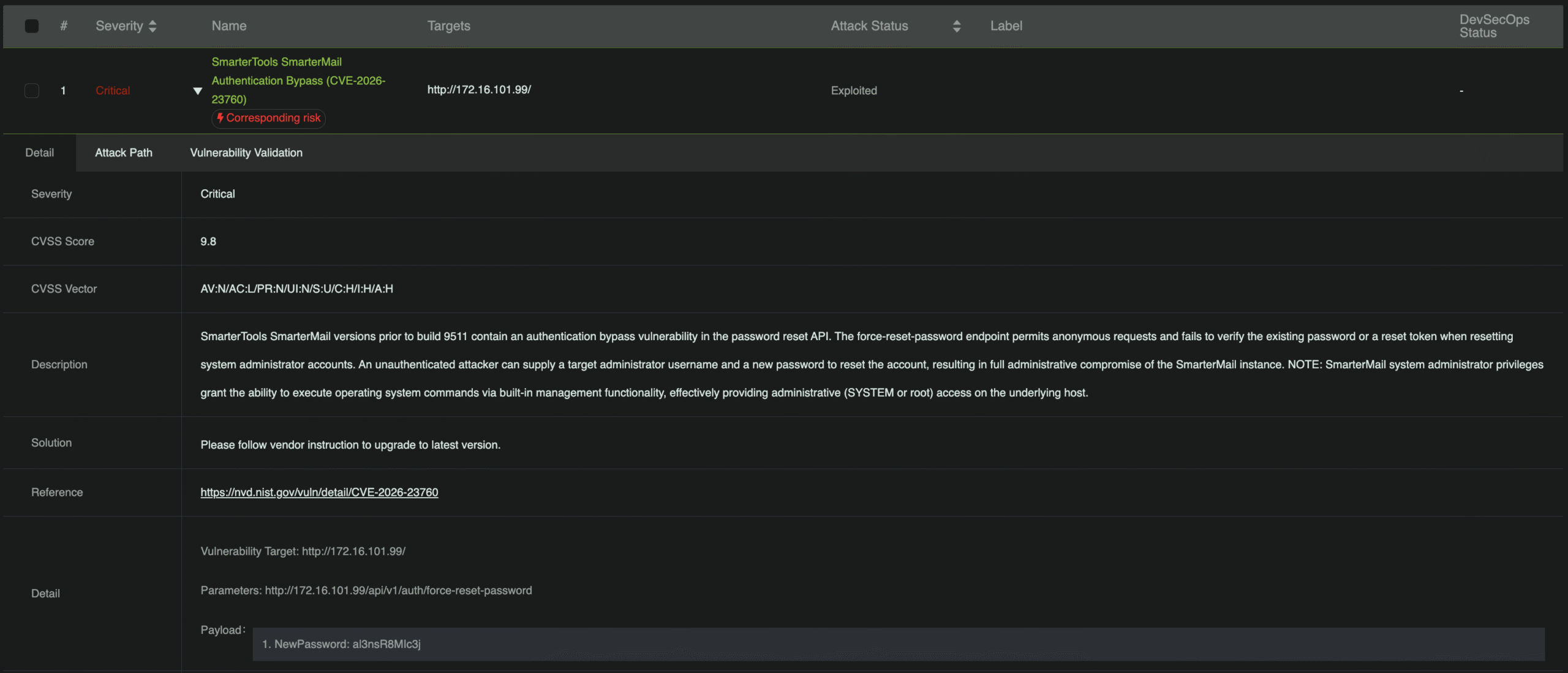
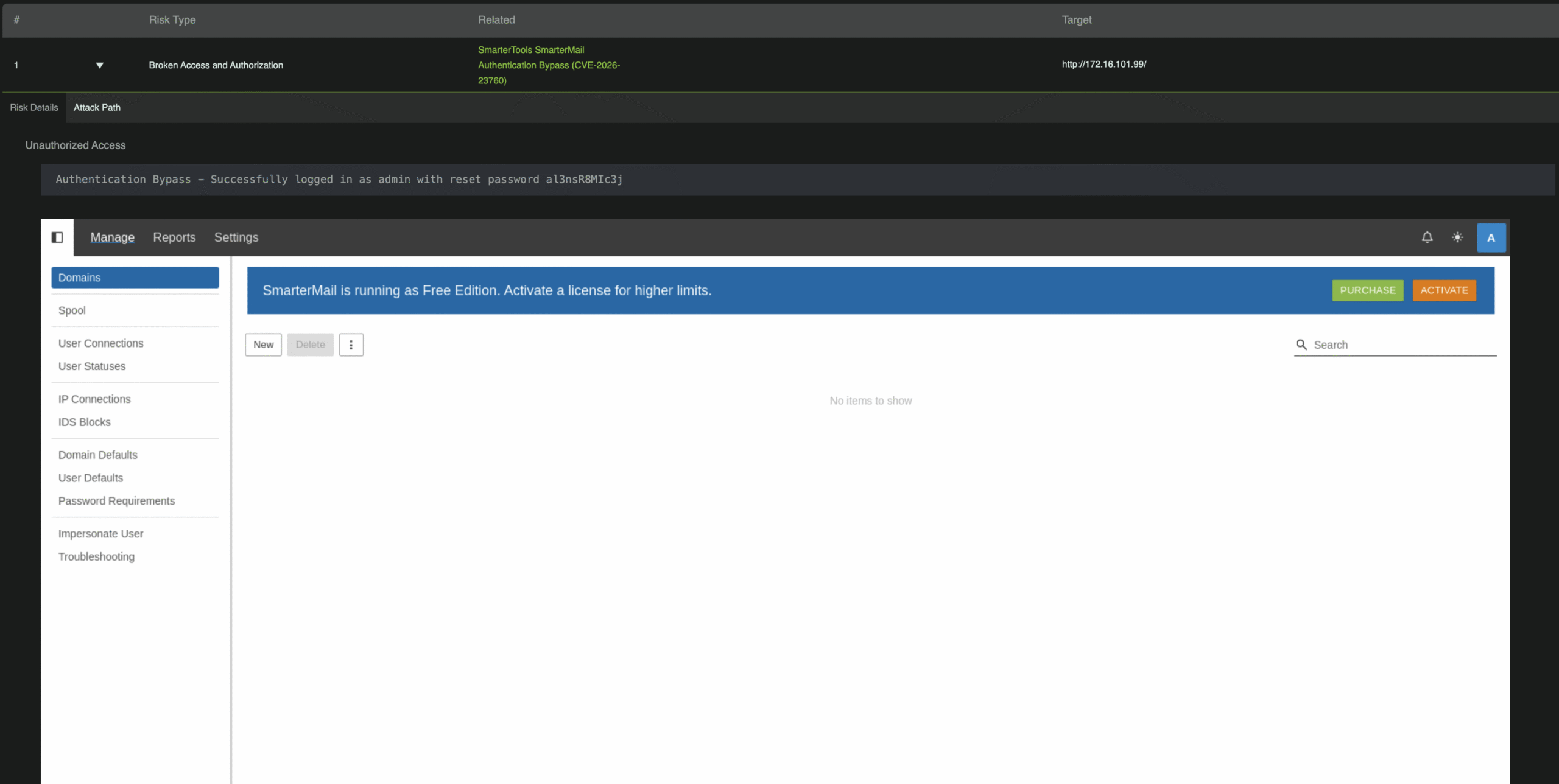
SmarterMail Authentication Bypass (CVE-2026-23760)
CVE-2026-23760 is an authentication bypass vulnerability that allows an unauthenticated attacker to reset the system administrator’s password via the /force-reset-password API endpoint. The issue stems from insecure logic in the password reset workflow, where attacker-controlled inputs—such as IsSysAdmin, Username, and NewPassword—are accepted without authentication or validation of the existing password. An attacker can submit a request with a known administrator username to take over the account, then abuse built-in functionality to execute operating system commands, providing a direct path to full remote code execution.
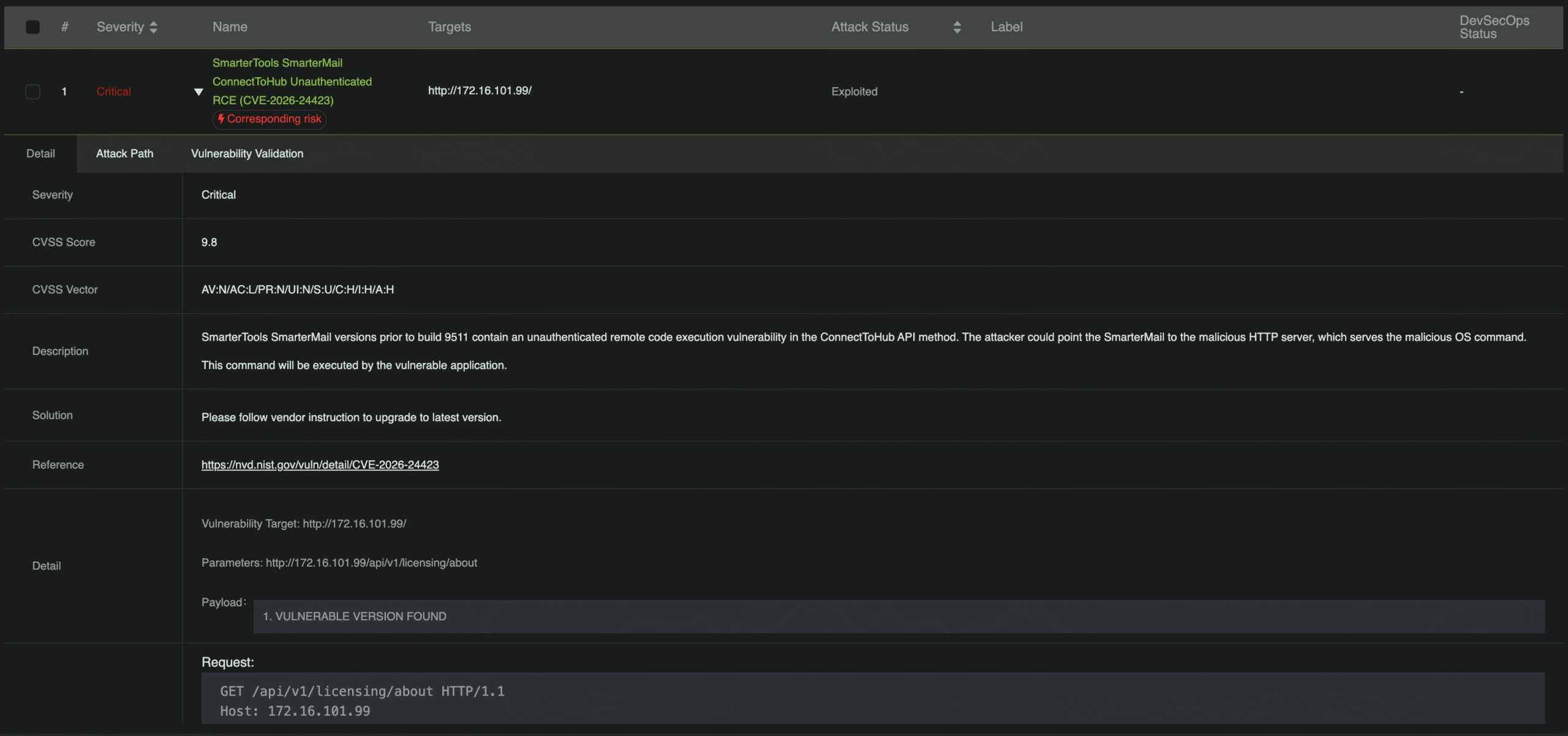
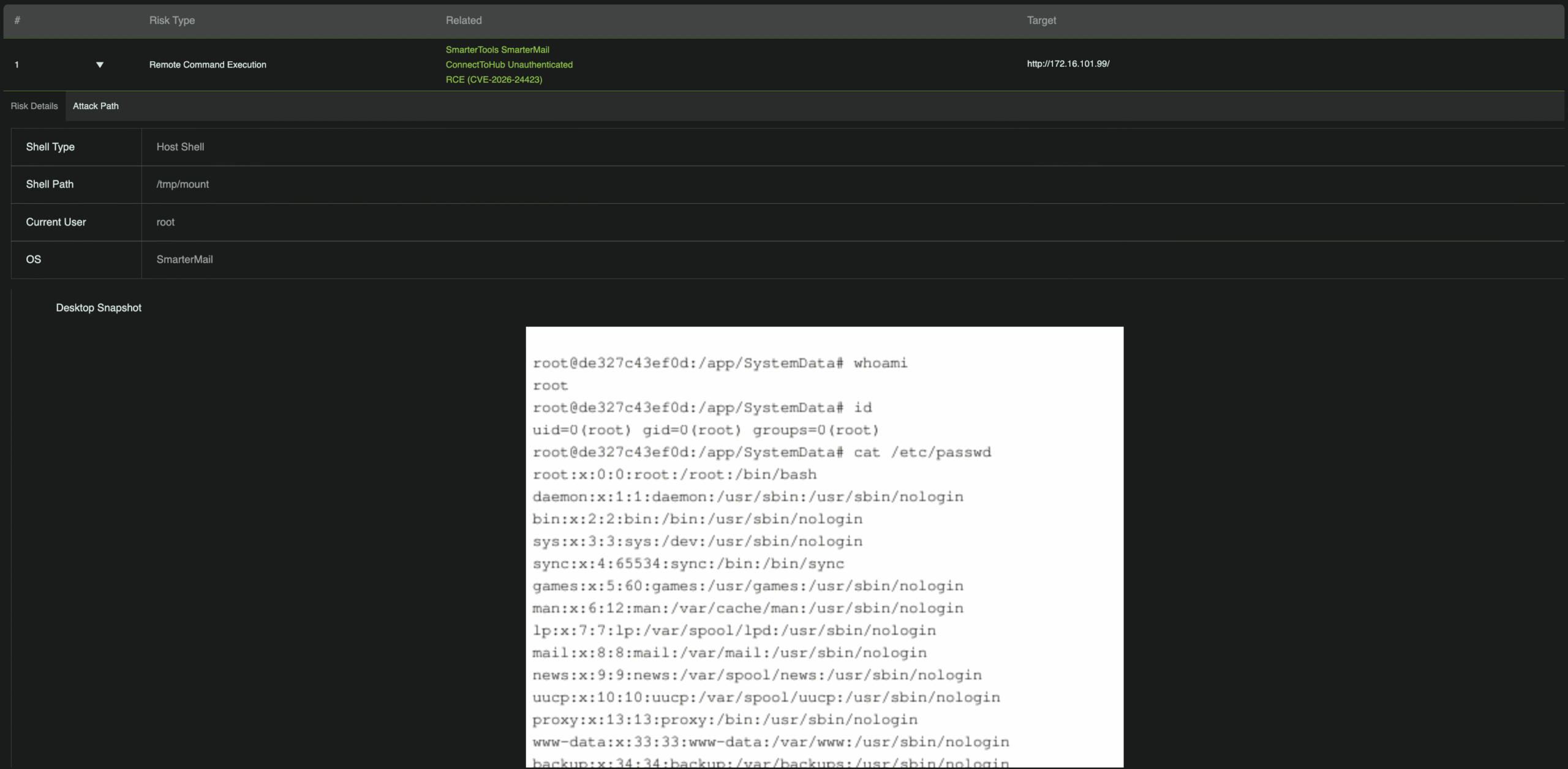
SmarterMail ConnectToHub Unauthenticated Remote Code Execution (CVE-2026-24423)
CVE-2026-24423 is a critical pre-authentication remote code execution vulnerability caused by an exposed /api/v1/settings/sysadmin/connect-to-hub endpoint. SmarterMail fails to enforce authentication and improperly trusts configuration data from a remote hub server. By supplying malicious fields such as SystemMount or CommandMount, an attacker can trigger OS-level actions without credentials. The risk is amplified in containerized environments with writable bind mounts, potentially leading to data loss, persistence, or service disruption.
Attack Chain:
1. Malicious hub setup: Attacker creates a fake hub API returning a crafted configuration payload with embedded commands.
2. Unauthenticated trigger: Target server sends a POST request to /api/v1/settings/sysadmin/connect-to-hub with the attacker’s hub address.
3. Trusted configuration retrieval: The server downloads and accepts the remote configuration without verification.
4. Command execution: SmarterMail processes malicious fields, executing OS-level commands and granting remote code execution.
Conclusion
With multiple critical flaws enabling authentication bypass and remote code execution, organizations using SmarterMail should patch immediately to reduce their attack surface. Just as importantly, validate your defenses: RidgeBot provides automated penetration testing that covers detection for all three CVEs discussed, helping security teams identify exposure early and remediate before attackers can exploit it.
