Cisco recently disclosed several critical vulnerabilities in Catalyst SD-WAN Manager, some of which are actively being exploited in the wild. As a result, CISA has added these flaws (CVE-2026-20128, CVE-2026-20133, and CVE-2026-20122) to its Known Exploited Vulnerabilities (KEV) Catalog, highlighting the immediate risk to network infrastructure.
CVE Breakdown
CVE-2026-20128 (CVSS 7.5): Unauthenticated Information Disclosure
This vulnerability stems from improper protection of Data Collection Agent (DCA) credential files, allowing a remote attacker to send a crafted HTTP request to read the password and gain DCA user privileges.
CVE-2026-20133 (CVSS 7.5): Unauthenticated Information Disclosure
Insufficient file system access restrictions allow an unauthenticated remote attacker to view sensitive information on the underlying operating system through the API.
CVE-2026-20122 (CVSS 7.1): Authenticated Arbitrary File Overwrite
Improper file handling in the API interface allows an attacker with read-only API credentials to upload a malicious file, overwrite arbitrary files, and gain vManage user privileges.
Attack Sequence
Threat actors chain these vulnerabilities to achieve full system compromise through the following sequence:
1- Credential Extraction: Exploiting CVE-2026-20133/20128 to leak DCA authentication keys.
2- Authentication: Logging in with extracted DCA credentials to obtain a valid authenticated session.
3- File Upload & Deployment: Using directory traversal (CVE-2026-20122) to upload and deploy a malicious webshell to the WildFly directory.
4- Execution: Achieving remote code execution (RCE) with system privileges.
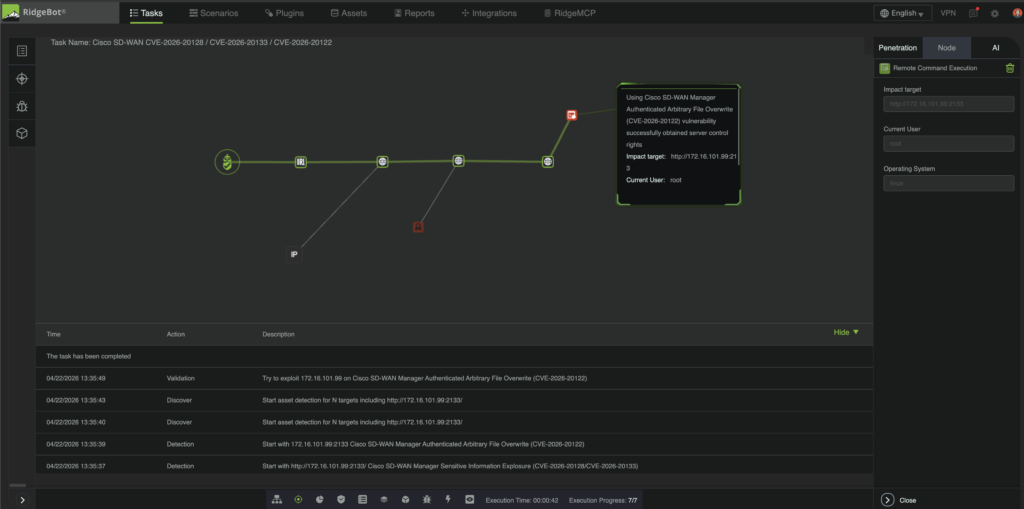
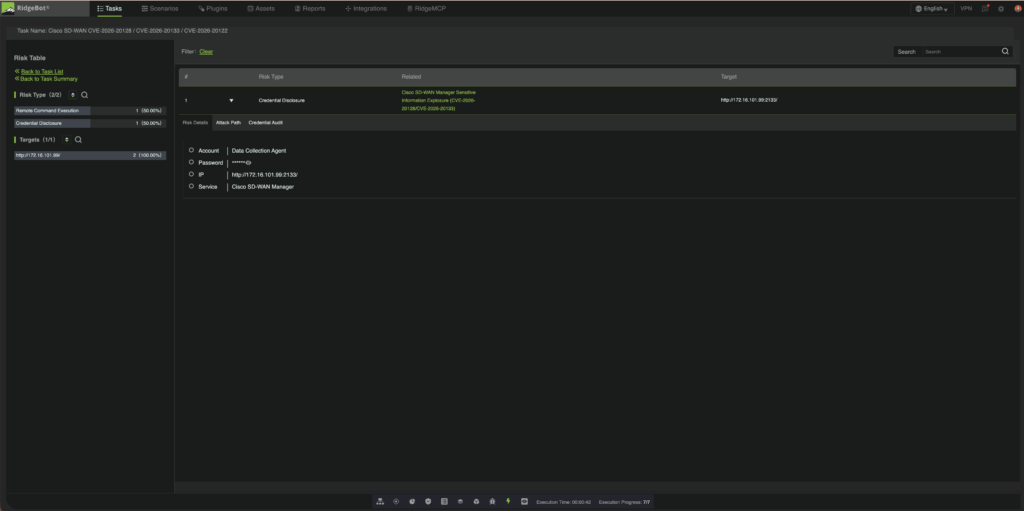
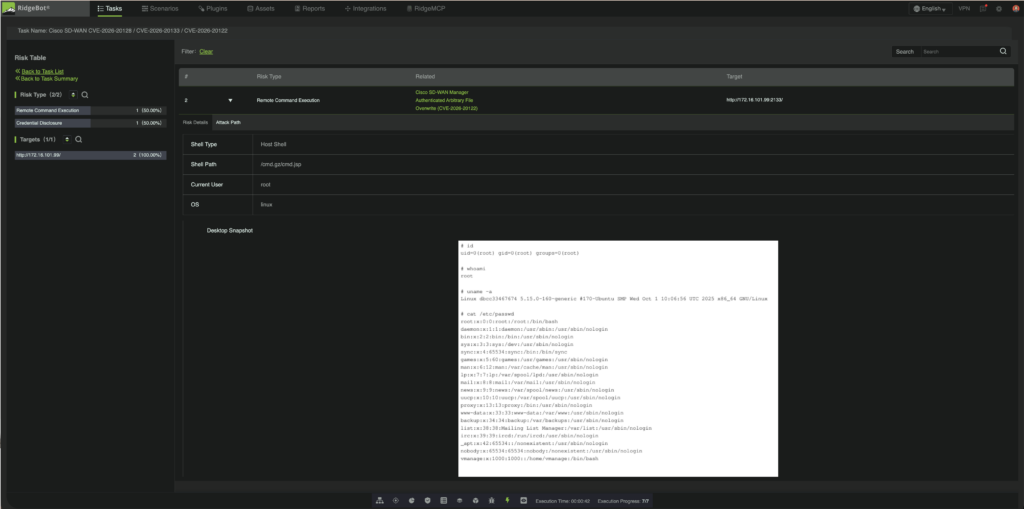
Detection and Exploitation on RidgeBot
The following figures demonstrate how RidgeBot detects vulnerable behavior and confirms successful exploitation through the full attack chain.
RidgeBot effectively identifies and retrieves DCA credentials by leveraging the unauthenticated information disclosure vulnerabilities (CVE-2026-20133 and CVE-2026-20128).
RidgeBot exploits directory traversal (CVE-2026-20122) to deploy a malicious webshell, achieving RCE. Successful exploitation is confirmed via a reverse shell from the Cisco SD-WAN server, providing the attacker with full command execution and system control.
Technical Impact and Remediation
Successful exploitation of the chained vulnerabilities can lead to full compromise of the network infrastructure. An attacker can first obtain elevated privileges, moving from DCA access to vManage operating-system level privileges, ultimately achieving administrative control and remote code execution across the SD-WAN management plane.
Organizations should immediately upgrade affected systems to a fixed software release and restrict exposure of management interfaces to trusted networks only. Because this vulnerability is actively exploited in the wild, passive scanning alone is not sufficient.
RidgeBot provides active validation to safely confirm real exploitability, including remote code execution paths, enabling security teams to prioritize patching and protect exposed environments before attackers can take advantage of the flaw.