Overview
Ridge Security recently conducted a survey among 75 global users and partners with 32% from America, 35% from Europe and 23% from Asia Pacific.
We share the results of the survey to shed some light on what the biggest driver is to move customers from manual-based to robot-based automated penetration testing and where specifically, customers are putting their focus on with respect to penetration testing.
Highlights
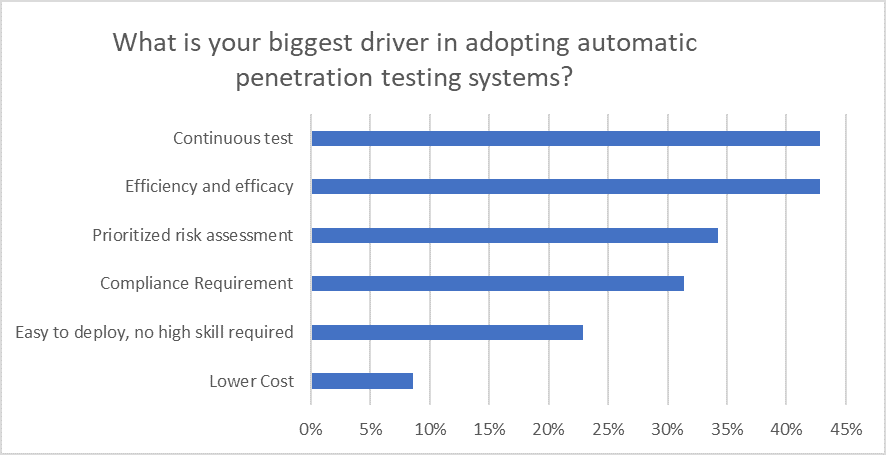
From our survey, the top three drivers for adopting automatic penetration testing systems are:
- Continuous testing
- Efficiency and efficacy
- Prioritized risk assessment
Penetration testing is not a one-off; it needs to be systematic and continuous in order to ensure the integrity of networks and its critical assets. And to do this in the most efficient way, admins need automated tools that deliver high efficacy, with assessments that prioritize risk.
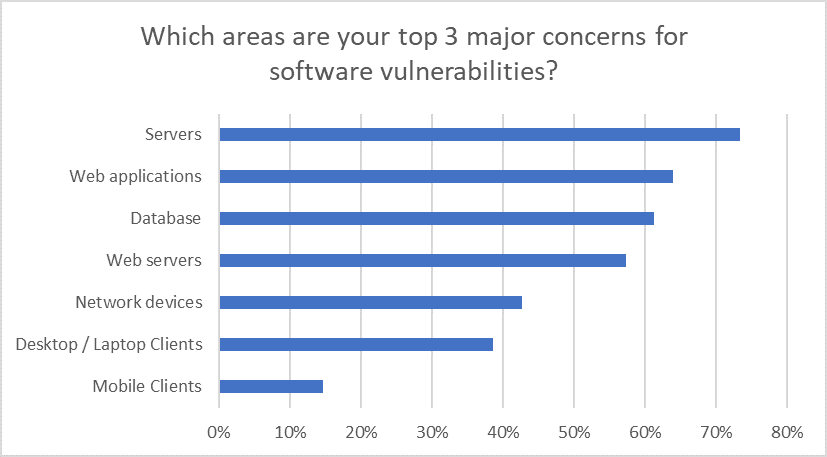
The need for automated penetration testing is becoming more and more clear to organizations. The top three areas of focus, according to our survey, include:
- Servers
- Web applications
- Databases
Servers can be secured at the operating system and networking level, but given today’s expanding attack surface, and digital and access point proliferation, the exposure to risk is extremely high. In a world of SaaS, e-commerce, any software of significant size will contain bugs, and web applications are no exception. Databases are also prone to exploitation, because they contain the key target for all hackers – data – specifically, confidential data. After breaking through past servers, databases are the next critical targets.
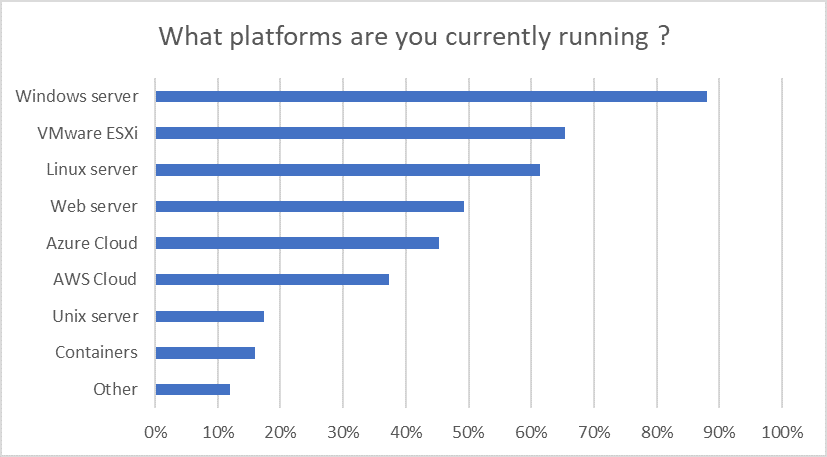
And from a production environment, the majority of our participants are currently running these platforms:
- Windows® Servers
- VMware ESXi
- Linux
All platforms contain their unique vulnerabilities and staying on top of patches is an important part of any security strategy.
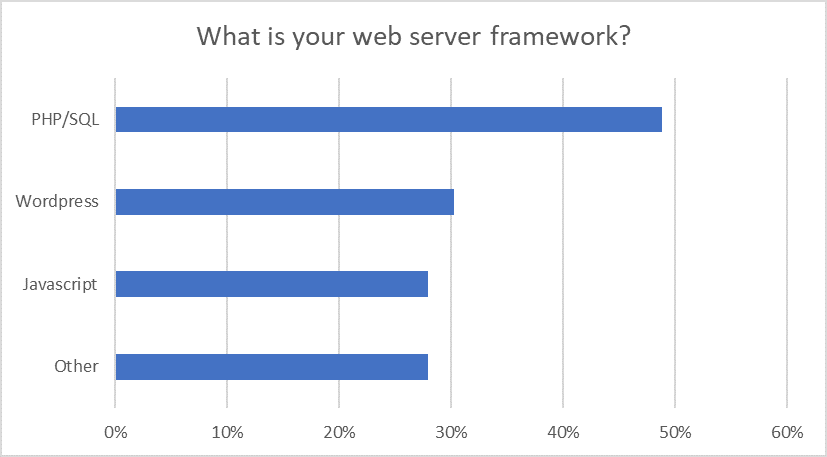
Drilling into the specifics of web servers, the top web server frameworks include:
- PHP/SQL
- WordPress
- Javascript
Any security measure to protect web services needs to be proactive and deliberate, since there are many security loopholes and pitfalls in web server security.