PaperCut MF is a cost-effective, multi-platform software solution designed for schools, libraries, and businesses globally. It manages, accounts, and recovers print, copy, fax, and scan output through user login or card ID. Currently employed by over 100,000 sites in 100+ countries, PaperCut MF stands as a leading global print management solution, extending its functionality to off-the-glass Copy, Fax, and Scan tracking at multifunctional printers (MFPs) via embedded/on-board applications.
In March and August 2023, PaperCut grappled with critical vulnerabilities—namely CVE-2023-27350 and CVE-2023-39143. These vulnerabilities presented substantial threats to organizations relying on PaperCut NG/MF software, prompting the company to respond proactively by releasing updated versions that addressed these critical security issues.
The first vulnerability, CVE-2023-27350, exposed a risk of remote code execution in PaperCut NG/MF software, potentially compromising the security of the application server. Affected versions spanned from 8.0.0 to 22.0.8. The second vulnerability, CVE-2023-39143, posed a critical risk for PaperCut NG/MF running on Windows systems prior to version 22.1.3. This vulnerability could lead to unauthorized access and manipulation of data on affected Windows systems.
As of April 19, 2023, PaperCut became aware of the active exploitation of the CVE-2023-27350 vulnerability in the wild. In response, they promptly published additional details, including indicators of compromise such as log file entries, known malicious domains, and YARA rules to detect observed malicious activity.
The recent identification of vulnerabilities in PaperCut MF/NG, exemplified by CVE-2023-27350 and CVE-2023-39143, underscores the critical need for robust risk and vulnerability management within organizations to safeguard against persistent cyber threats. Ridge Security has proactively responded to this challenge by developing RidgeBot® plugins designed to identify and address these vulnerabilities before they pose a threat to organizations.
RidgeBot, a comprehensive cybersecurity tool, is equipped with plugins that target a wide range of potential exposures across an organization’s digital landscape. Notably, our plugin library now incorporates capabilities to detect and address CVE-2023-27350 and CVE-2023-39143 in PaperCut MF/NG. The provided screenshots below showcase RidgeBot in action, revealing its capacity to identify the PaperCut vulnerabilities, detailed attack logs, and evidence of successful exploitation.
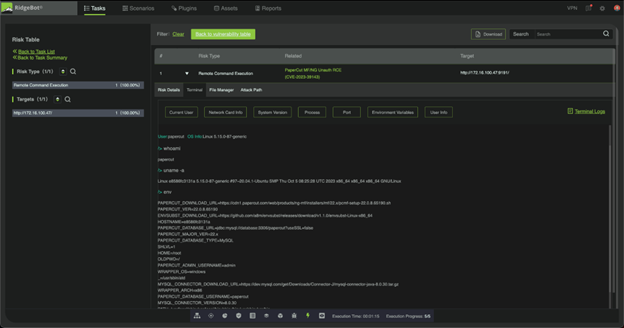
Fig1: RidgeBot discovers Papercut vulnerability
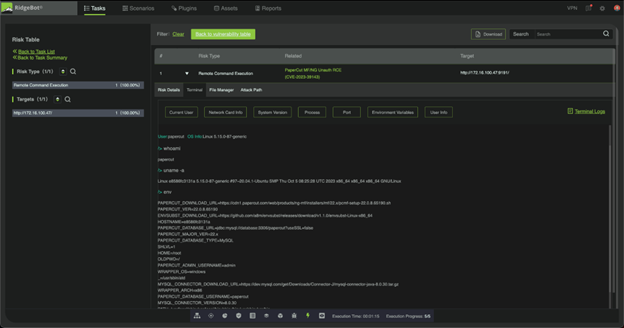
Fig2: RidgeBot Papercut Attack logs
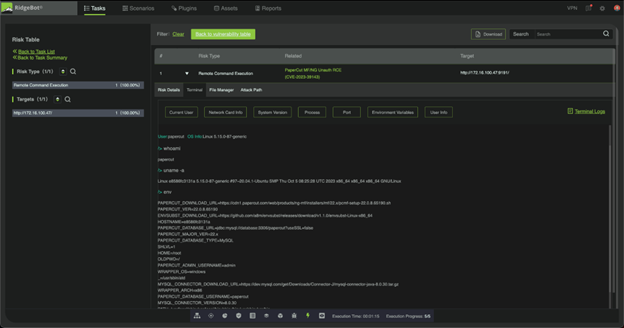
Fig3: RidgeBot showing evidence of exploit being successful
RidgeBot automated penetration testing is your essential defense against vulnerabilities akin to those observed in the recent PaperCut incident. Even systems like printers can harbor vulnerabilities that cybercriminals can exploit to gain access to sensitive data.
RidgeBot is a crucial ally for all organizations, helping uncover weaknesses, vulnerabilities, and exposures in digital assets. It significantly shortens the window for hackers to strike, condensing their opportunities from months to hours. This is achieved through strategic tests during network changes, new application releases, or adjustments in printer user groups.
Ridge Security specializes in outsmarting cybercrime. RidgeBot’s core relies on collective threat intelligence, vulnerability insights, and AI decision-making. Using advanced ethical hacking techniques, RidgeBot mimics a real attacker. It diligently identifies, exploits, and documents findings.
RidgeBot detects attack vectors, confirms vulnerabilities, and suggests actionable steps for remediation, all before hackers exploit them. Continuous, automated testing empowers defenders to proactively strengthen digital security, especially concerning printers. Plus, it’s user-friendly, accessible to those with solid IT proficiency.
To understand how RidgeBot can enhance your defenses, click here to get in touch.
By Vincent Qi, Ridge Security Researcher