by Ridge Security Marketing | May 6, 2020 | Automated Pen Test Demo
On April 22nd, Washington Post reported nearly 25,000 email addresses and passwords allegedly from NIH, WHO, Gates Foundation, and others, are dumped online. According to a cybersecurity expert, 48 people from WHO have ‘password’ as their password. Others had used...

by Ridge Security Marketing | Apr 30, 2020 | Pen Test Technical Tips
In part one, we introduced “stealthier” Windows-based tools to detect MSSQL service: detect MSSQL instance based on the working group and detect MSSQL instance in a windows domain environment. In this blog, we share the Exploit of MSSQL, enable the target...
by Ridge Security Marketing | Apr 20, 2020 | AI in Automated Pen Test
CAPTCHAs—Completely Automated Public Turing test to tell Computers and Humans Apart. To train a computer or “robot” to become an ethical hacker is not a trivial task. The obvious question that comes to mind is, “how can it pass CAPTCHAs—automated...

by Ridge Security Marketing | Apr 20, 2020 | Pen Test Technical Tips
In penetration testing, we often encounter an MSSQL database. Usually, we will use an extended procedure like xp_cmdshell to perform privilege escalation or execute system commands. However, when xp_cmdshell is unused, what other methods can we leverage? We are...
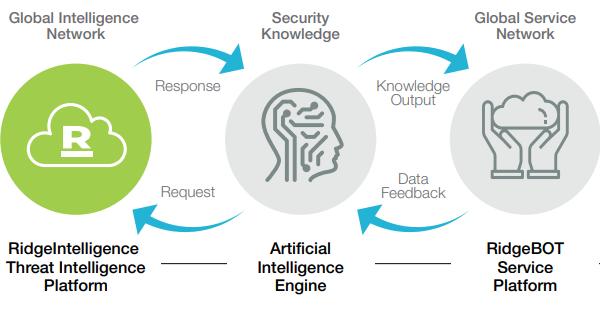
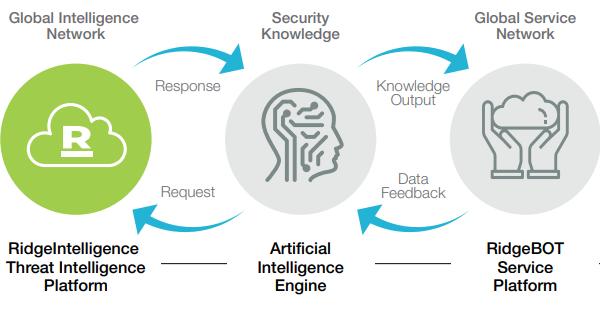
by Ridge Security Marketing | Apr 13, 2020 | RidgeBot
Ridge Security is transforming Security Validation with RidgeBot, an Intelligent Security Validation Robot. RidgeBot’s are modeled using techniques utilized by literally millions of hackers that penetrate systems. When...